Make money easy
Monzo makes managing money as easy as 1-2-3.
1. See it all.
2. Save more.
3. Spend confidently.
See your finances like never before
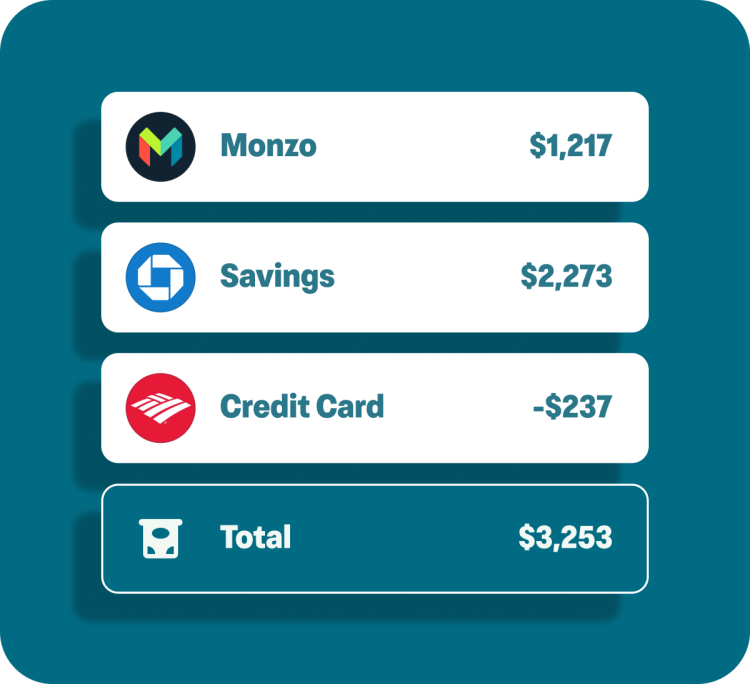
All your banks, one app
Control all your accounts and spending from the Monzo app.

Understand your money
Easily track your income, spending, and savings to know where your money is going.
Save more to meet your goals
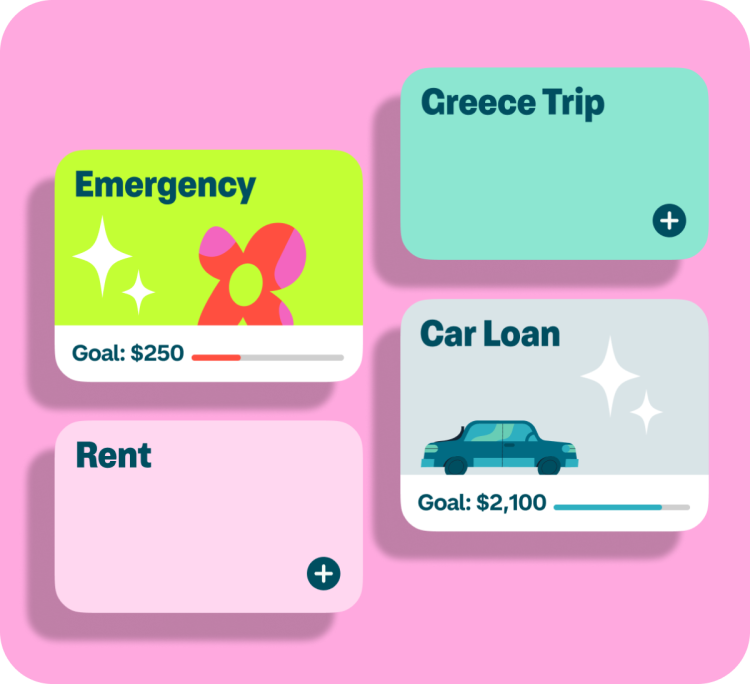
Reach your goals
Keep your savings separate from your balance to reach your goals—whether you’re building an emergency fund, saving for a vacation, or something else!
Saving made easy
Set aside money automatically from each paycheck, or round up payments to the nearest dollar to save a little – often.
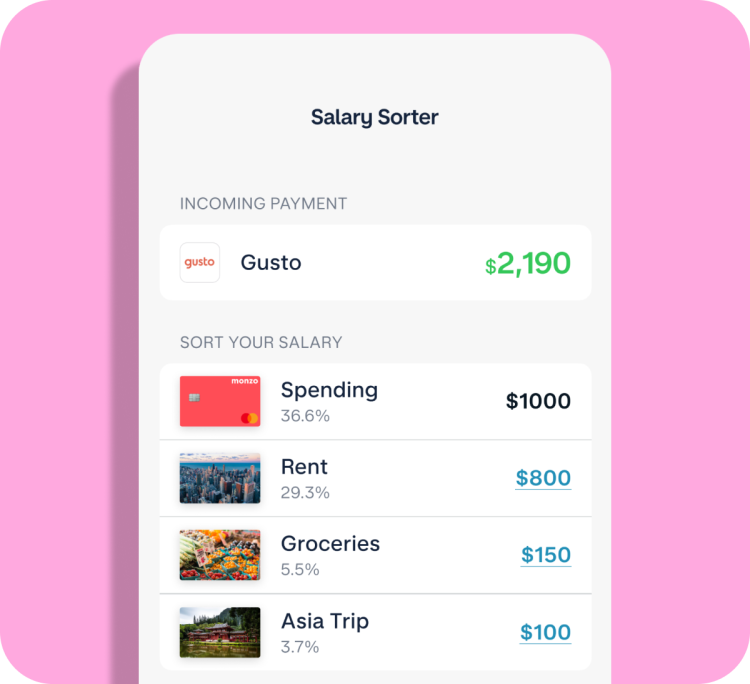
Spend with confidence

Keep spending on track
Gain peace of mind with instant spending notifications and a balance that’s updated in real time.

Pay your bills on time
Set aside money for future expenses such as rent or utilities. Then spend with confidence knowing the important stuff is taken care of.
Say goodbye to fees
🚫 No foreign exchange conversion fees
🚫 No overdraft fees
🚫 No monthly fees or account minimums
🚫 No ATM fees at 40,000 fee free ATMs

Safety first
With Monzo, your money is FDIC insured up to $250,000. And you can protect your account with biometrics or PIN. If something goes wrong, get help when you need it with 24/7 customer support.